9-12
74%
of attacks go undetected on average.
On average
We know more about cyber threats than anyone.
< 5 MIN
Threat detection and response is the biggest
obstacle for most security teams.
99%
COMPROMISES RESOLVED WITHOUT IR
Microsoft Defender for Endpoint
FireEye Endpoint Security
FireEye Network Security
FireEye Email Security
Sources: John E. Dunn, Damballa Analyssis 2014; Frost and Sullivan Global Information Security Workforce Study 2017; Mandiant 2020 Security Effectiveness Report, April 2020


On average
full-time employees are needed to run the average 24/7 SOC.
1
2
3
4
5
6
INITIAL
RECONNAISANCE
INITIAL
COMPROMISE
FOOTHOLD
ESTABLISHED
PRIVILEGES
ESCALATED
INTERNAL
RECONNAISANCE
MISSION
COMPLETE
PRE-BREACH
POST-BREACH
SECURITY TECHNOLOGY
MANAGED DETECTION AND RESPONSE SERVICES
Once an attack evades early detection, organizations need skilled people to hunt attackers hidden within the network.
FireEye Cloud Security
FireEye Helix
1 HOUR
MEDIAN TIME TO
INVESTIGATE AND RESPOND
Join forces with Mandiant Managed Defense.
How MDR with frontline experts works.

KNOWLEDGE OF THE ATTACKER

VISIBILITY ACROSS
THREAT VECTORS

Breach intelligence?
Product telemetry?
Adversary intel?
The breadth of an attack
Across endpoint, network,
cloud and email?
Spot hidden attackers?
Reduce dwell time?
Respond before your business is impacted?
Prevent repeat attacks?
Does your team have what it takes
to detect and respond to advanced attacks?
Frontline cyber security expertise
MANDIANT THREAT INTELLIGENCE
Proactive threat hunting
Alert prioritization and enrichment with needed context
Rapid investigation, containment and response
Effective protection from advanced ransomware threats
Ongoing assessment and recommendations
security technology
Start with endpoint

and/or
security technology
Add visibility
detection
Prioritize and enrich with threat intelligence
Around-the-clock monitoring
Alert triage by a Mandiant expert within 5 minutes
Enrich prioritized alerts with needed context
detection
Proactively hunt for hidden adversaries
Hunt missions defined by Mandiant frontline knowledge
Understand attacker behavior as mapped to MITRE ATT&CK®
Follow mission activity and get related threat intel
RESPONSE
Rapid investigation and containment
Reduce impact immediately by containing affected hosts
Scope attackers' abilities and anticipate their next move

RAPID
RESPONSE

PROACTIVE THREAT HUNTING








RESPONSE
Accelerate response
Leverage the full force of Mandiant to quickly respond without the added cost of a full incident response.
Investigation - Response in minutes, not hours


Advanced Practices and Malware Reverse Engineering support

10,000
alerts are received by most security operations teams daily.









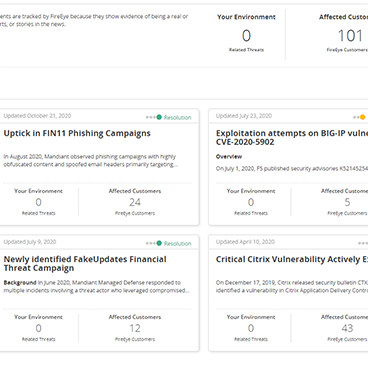
See what Mandiant experts see. Explore six views of your customized Managed Defense portal.
PREVIEW Managed Defense.






4. Hunting Dashboard

3. Community Protection Events Dashboard

2. Incident Detail

1. Managed Defense Dashboard
View Dashboard
4. AEDA Dashboard
View Dashboard
3. TAAM Dashboard
View Dashboard
2. MITRE ATT&CK Dashboard
View Dashboard
1. Effectiveness Dashboard

Follow threat hunting campaigns as they unfold in your environment.
Navigate mission activity using the MITRE ATT&CK® matrix and review published investigations from hunt missions.
Threat Hunting Dashboard

You benefit from situational awareness of emerging threats Mandiant is tracking.
When Mandiant experts identify broad-reaching threats, we initiate a Community Protection Event to keep you protected and updated on all associated intelligence.
Community Protection Events Dashboard


You receive a detailed summary report for all alerts that result in investigation.
This report provides threat context and links you to related intelligence on Mandiant Advantage.
Each investigation includes remediation recommendations, lists affected assets and provides detailed investigation findings.

Interact with Mandiant experts as they protect and defend through your customized Managed Defense portal.
Your dashboard lists the volume of threats by source and severity and links you to recent investigation reports.
View everything Mandiant experts are seeing and doing in your environment, in real time.
Managed Defense Dashboard


















5. Hunt Detail


6. Hunt Mission Details
Dig into threat hunting campaigns, navigating by MITRE ATT&CK® matrix or by mission.
View the ATT&CK tactic and techniques leveraged in the hunt and see relevant device for each hunt.
Threat Hunting Detail

Gain threat hunting insight through Mission Details. Review the Mandiant hunt team's hypothesis and description of what experts are looking for.
See the full mission scope defined by MITRE ATT&CK® technique. Link directly to Mandiant Advantage for related threat intelligence supporting the mission.
Hunt Mission Details




















AVERAGE TIME FROM
ALERT TO TRIAGE
View Dashboard
4. AEDA Dashboard
View Dashboard
4. AEDA Dashboard
Incident Detail


Can your team access:
Can your team see:
Can your team:
Can your team:










Roll over boxes to see more.

LEARN MORE
PROTECT anD DeFEND YOUR BUSINESS
WITH FRONTLINE EXPERTS
MANDIANT MANAGED DEFENSE



CONTACT AN EXPERT

Want to learn more?


INTRODUCTION
Mandiant Security Validation
Formerly Verodin
See how we do it

Cybersecurity is a Relevant Business Metric…

business continuty

REGULATORY COMPLIANCE

PROTECTION OF ASSETS

RATIONALIZATION & OPTIMIZATION
Across all industries, businesses rely on critical assets to generate revenue, deliver services, be competitive, and drive value. Significant investments are made to ensure their protection.
• Access to Data
• Consumer Services
• Critical Infrastructure
• Laws & Regulations
• Accreditations
• Privacy
• Critical Data
• R&D
• Intellectual Property
• M&A
ROI Analysis
Controls Prioritization
Evidence of Effectiveness
•
•
•
53%
Companies are completely missing or unaware of executed attacks
74%
of attacks go undetected
On average
9%
of alerts are correlated by SIEMs
Only
> Primarily due to broken processes & misconfigured tools…
> No events, alerts or awareness that something is/has happened
WHY MANDIANT SOLUTIONS
We know more about cyber threats than anyone
850
Research demonstrates how little visibility most security teams have into ongoing threats...
Engagements
200K
Hours
Responding to Attacks
Per Year
Machine Intelligence
15,000 network sensors
56 countries
Tens of millions of malware detonations per hour
Adversary Intelligence
23 countries
30+ languages
180+ analysts and researchers
30K intel reports per year
Managed Defense
5 Security Operations Centers
99M+ events ingested
21M+ alerts validated by Intel
Expertise
13+ years of investigative expertise
26 countries with consultants
400+ Red Team Exercises Per Year


SECURITY VALIDATION
INCIDENT
RESPONSE
ADVERSARY
AWARENESS
CORRELATED
CAMPAIGN
ACTIVITY
GLOBAL
ATTACK
VISIBILITY











MEASURE
OPTIMIZE
RATIONALIZE
MONITOR

Effective Defenses
Threat Actor Assurance
Infrastructure Health
Framework
Assessments
Executive Reporting
Rationalize
Investments