

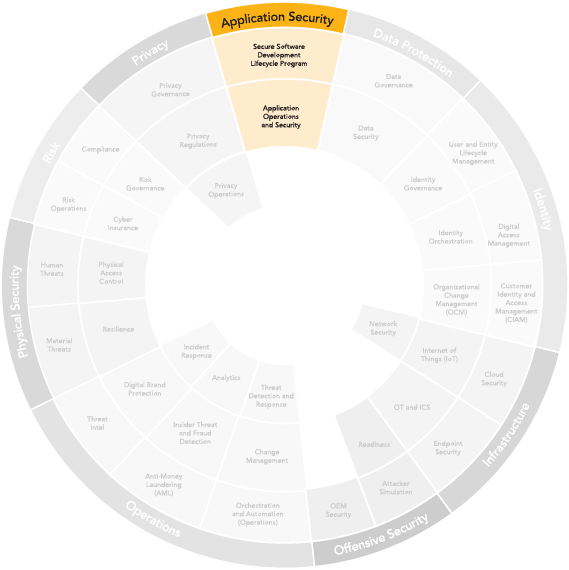
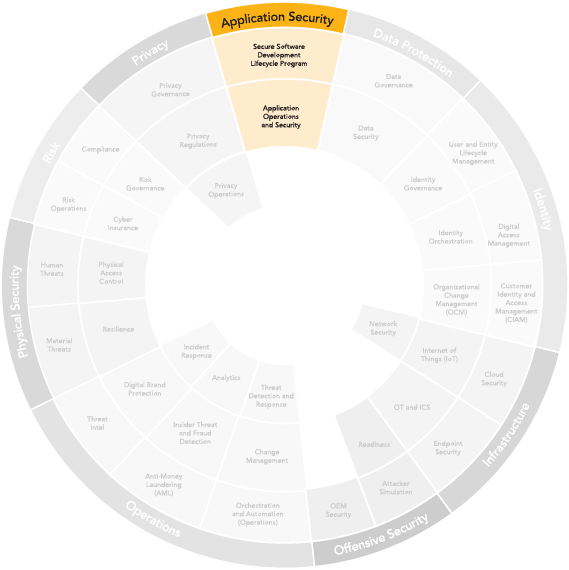
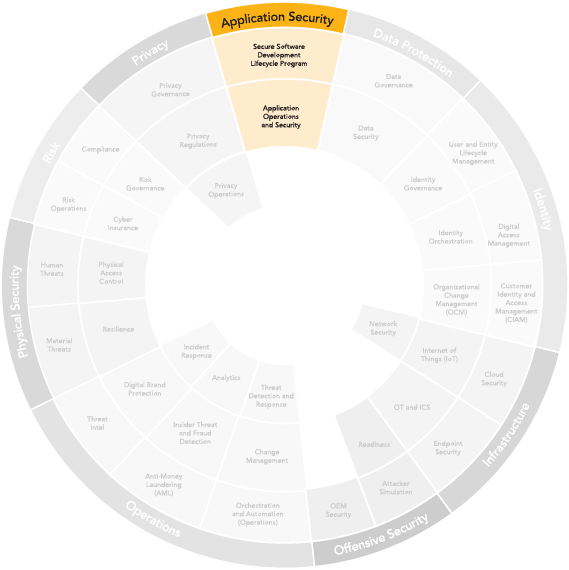
Optiv Market System
TM
Real intel. Real insights. Real decisions. See your cyber program clearly with Optiv Market System™


Privacy
Protect information from unauthorized access, use or disclosure.
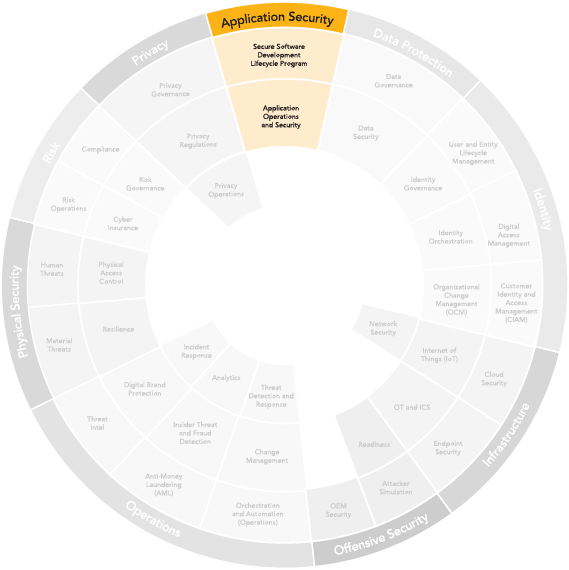
Application Security
Develop secure and resilient applications.
Data Protection
Identity
Protect digital identities from unauthorized access, use or theft.
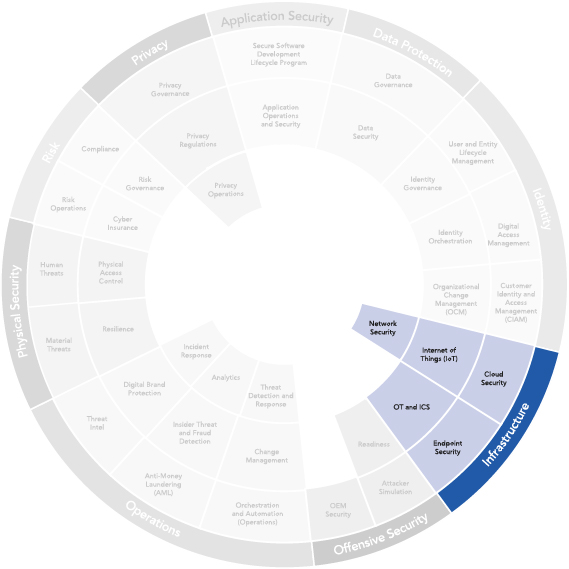
Infrastructure
Protect the systems that support your organization.


Risk
Identify, assess and mitigate potential risks with greater speed and accuracy.
Physical Security
Protect physical assets from unauthorized access, theft, damage or destruction.
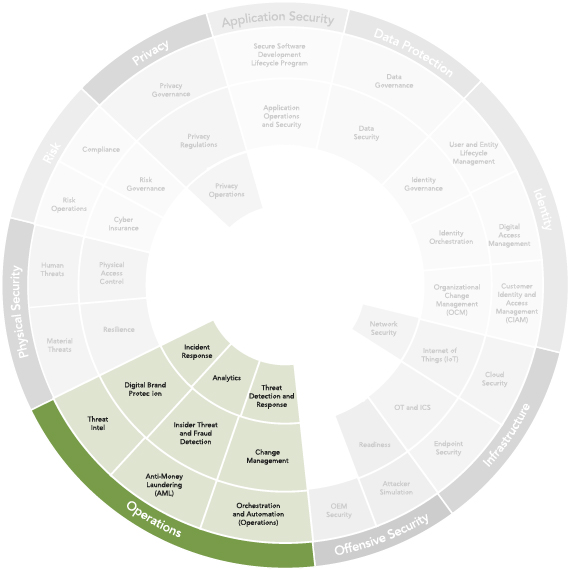
Operations
Optimize policies, procedures and controls to protect your organization’s assets.
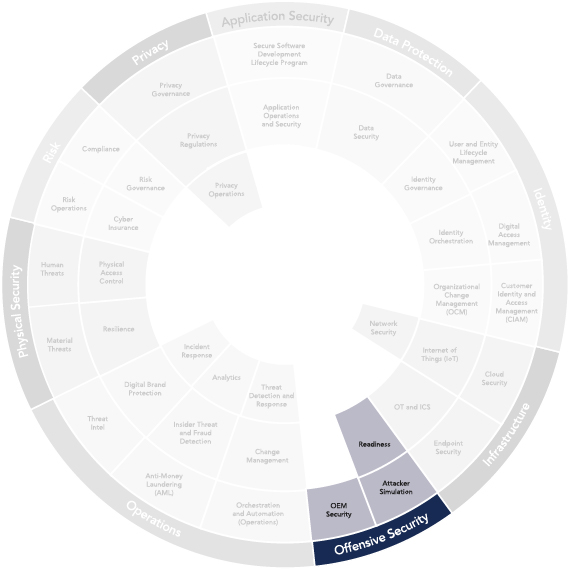
Offensive Security
Active testing and attacking of systems helps to identify vulnerabilities.






Application Security
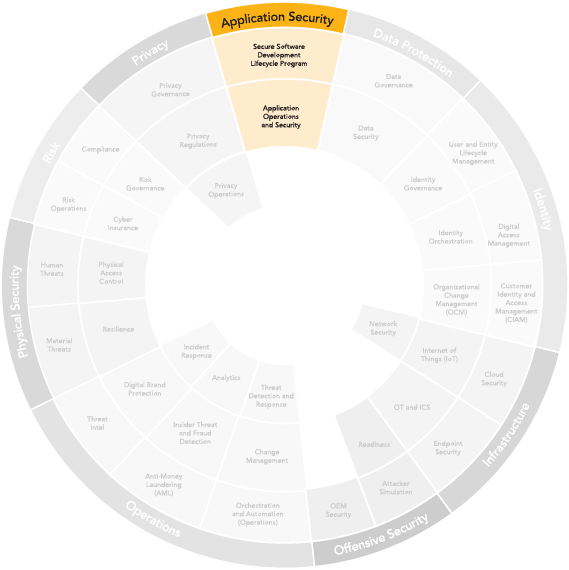
Reduce application risks through secure software development programs that continuously detect and address application vulnerabilities and ensure regulatory compliance.
Benefits of Application Security
Common Challenges
Critical Questions
Real-World Breaches
AppSec Domains

Applications and APIs are the leading sources of security incidents and attacks on AI applications are increasing
Automated AppSec scanners and tools generate false positives and fail to offer actionable insights
Organizations struggle to meet regulatory requirements and balance development velocity and security
Have you tested and secured business-critical AI applications and third-party components?
Do you have visibility into all APIs in your environment and the regulatory impact of API exposure?
Are you incorporating security into your application architecture and software development lifecycle (SDLC)?
2.9 billion records were stolen due to sensitive file exposure on a public web application
700 million user profiles exposed via unauthorized API scraping
Personal account information of 37 million subscribers exposed due to lack of strong API authorization controls
Secure Software Development
Lifecycle Program Application Operations and Security
Improved Security Posture Reduce overall risk and cost of potential data breaches by securing sensitive applications.
Reduce Development Costs Continuously test and secure code prior to release.
Ensure Regulatory Compliance
Comply with regulatory standards, including PCI, NIST, CCPA and GDPR.







Data
Protection
Benefits of Data Protection
Common Challenges
Critical Questions
Data Protection Domains
Data Protection Technology Partners
Real-World Breaches
Utilizing security controls and policies to ensure protection of digital data from unauthorized access, theft, corruption or other forms of damage.
Data protection involves implementing measures such as encryption, access controls and backup and recovery procedures to ensure sensitive information remains confidential, available and accurate.
Proactive Data Loss Prevention Implement effective controls, processes and health checks to ensure effective data protection.
Enables Data Privacy
Enable comprehensive data management to support privacy programs and reduce the risk and cost of data breaches.
Streamlines Compliance
Facilitate policies and programs to comply with data protection laws and standards.
Lack of data insights and ineffective data security controls can expose organizations to risk of data breaches
Failure to define and enforce data policies can result in regulatory noncompliance, fines and legal action
Ineffective data governance can result in poor data quality and high operational costs
Are you effectively identifying, collecting, retaining and managing sensitive data within your organization?
Can your data loss prevention program adapt to new technologies and compliance requirements?
Do you have a data privacy and governance program needed to ensure compliance and respond to incidents?
Data Governance
Data Security
SSNs and medical records of 62.4 million students stolen by exploiting a token-replay vulnerability
Weak encryption was exploited to compromise 383 million customer records
Personal information of 16.6 million users stolen by exploiting encryption flaws


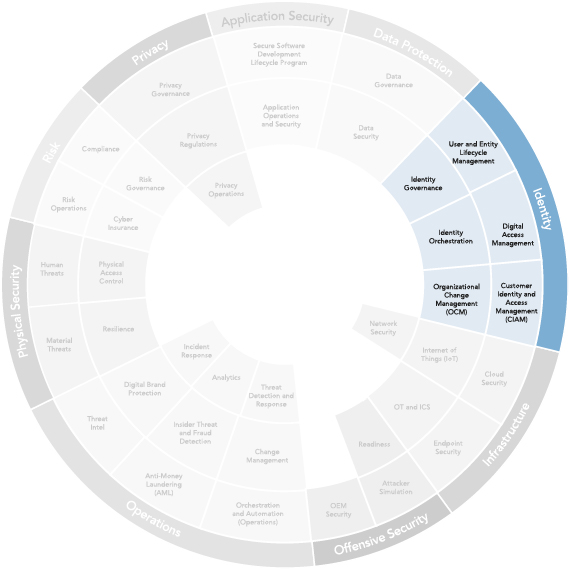
Identity
Benefits of Identity Security Controls
Common Challenges
Critical Questions
Identity Domains
Identity Technology Partners
Real-World Breaches
The protection of digital identities, such as usernames and passwords, from unauthorized access, use or theft. Implementation of security measures to ensure that only authorized individuals have access to sensitive information and systems, and identities are verified before granting access.
This includes using MFA, encryption and other security protocols to prevent identity theft, phishing attacks and other cyber threats that exploit vulnerabilities in identity management systems.
Access Control
Prevent unauthorized access to critical systems, ensuring the right users have the right permissions.
Risk Reduction
Minimize breach potential and support compliance through strong authentication and identity governance.
User Enablement
Deliver secure, seamless access across platforms without compromising productivity or experience.
Too many human and non-human identities across systems make it hard to manage access and enforce consistent security controls
Reliance on passwords or outdated methods increases vulnerability to unauthorized access
Limited insight into user behavior and entitlements hampers threat detection, auditing and compliance
Do you know who has access to what, and why they have it?
Are user permissions aligned with roles, responsibilities and the principle of least privilege?
Do you have visibility to detect and respond to identity misuse or compromise in real-time?
Secure Consumer Identity and Access Management (CIAM)
Digital Access Management
Identity Governance
Identity Orchestration
Organizational Change Management (OCM)
User and Entity Lifecycle Management
Details of 86 million customers leaked after threat actors gained access to user accounts that were not secured with MFA
Threat actors gained access to multiple customer environments in an SaaS environment via stolen credentials and exfiltrated data

Infrastructure
Benefits of Comprehensive Infrastructure Security
Common Challenges
Critical Questions
Infrastructure Domains
Infrastructure Technology Partners
Real-World Breaches
The protection of endpoints, systems and networks that support an organization's operations. This includes safeguarding hardware, software, data centers, cloud services and other critical components from unauthorized access, theft, damage or disruption.
Risk Reduction
Minimize attack surfaces across cloud, network, OT/IoT and endpoints.
Operational Continuity
Ensure systems stay online and functional via secured infrastructure layers.
Comprehensive Visibility
Gain visibility into all parts of infrastructure to detect anomalies and respond effectively.
Disjointed tools and teams create gaps in coverage across IT, OT, cloud and endpoint environments
Outdated infrastructure lacks modern security controls, increasing exposure to threats and limiting agility
Diverse infrastructure stacks create challenges in maintaining consistent security policies
Are you maintaining a current asset inventory and adjusting your security controls to protect it?
Do you have all the tools and processes to identify, investigate and contain threats across environments?
Is your infrastructure security evolving with emerging technologies, threats and regulations?
Cloud Security
Endpoint Security
Network Security
Operational Technology (OT) and Industrial Control Systems (ICS)
Internet of Things (IoT)
Attackers breached a water treatment facility and attempted to increase the chemical additives in an effort to poison the water supply
Attackers exploited a VPN to gain access to systems, shutting down critical infrastructure systems

Offensive Security
Benefits of Offensive Security
Common Challenges
Critical Questions
Offensive Security Domains
Offensive Security Technology Partners
Real-World Breaches


The practice of actively testing and attacking computer systems to identify vulnerabilities that could be exploited by malicious actors.
Offensive security involves simulating real-world attacks to find and fix security issues before they can be exploited by actual attackers and creating stronger security posture.
Improved Defenses
Prepares organizations for defending against real-world cyber attacks.
Reduced Insider Threats
Improved protection of systems and data reduces the likelihood of insider compromise.
Compliance and Risk Management
Demonstrate compliance with standards like PCI that mandate pen testing and similar activities.
Attack surfaces are growing and organizations are struggling to keep up
Vulnerabilities, misconfigurations and insider threats leave organizations exposed to attacks and theft
Organizations lack resources to meet proactive security requirements mandated by compliance standards
Have you evaluated your security controls against sophisticated real-world attacks and insider threats?
Are you aware of how publicly available information and social engineering can be used to compromise your organization?
Can you effectively prioritize and remediate vulnerabilities to reduce business risk and ensure compliance?
Attacker Simulation
Original Equipment Manufacturer (OEM) Security
Readiness
Unpatched vulnerability was exploited to breach 148 million records containing PII
885 million sensitive files were leaked by exploiting an application design error
560 million user records were exposed by exploiting accounts that lacked multi-factor authentication


Operations
Benefits of Operations Security
Common Challenges
Critical Questions
Operations Domains
Operations Technology Partners
Real-World Identity Breaches


The ongoing process of implementing and managing information security personnel, security policies, procedures and controls designed to protect an organization's digital assets from unauthorized access, use, disclosure, disruption, modification or destruction.
Faster Resolution
Reduce dwell time by accelerating detection, triage and response.
Proactive Defense
Leverage intel and analytics to predict, detect and disrupt threats.
Operational Consistency
Standardize workflows and responses through orchestration and automation.
High volumes of low-priority alerts slow response to real threats and strain security resources
Disconnected intel, detection and response efforts slow investigations and reduce effectiveness
Reliance on human-driven workflows delays response, increases errors and limits scalability
Are your detection and response workflows integrated across teams, tools and data sources?
Can you prioritize and respond to threats based on business risk, not just technical severity?
Where can automation reduce response time without sacrificing accuracy or control?
Analytics
Anti-Money Laundering (AML)
Digital Brand Protection
Incident Response (IR)
Insider Threat and Fraud Detection
Threat Detection and Response (TDR)
Threat Intelligence
Orchestration and Automation
A cloud misconfiguration led to the exposure of ~100 million customer records
Threat actors leveraged social engineering to gain access to systems and takeover accounts
Records for over 140 million citizens were breached due to unpatched critical vulnerabilities


Physical Security
Benefits of Physical Security Services
Common Challenges
Critical Questions
Physical Security Domains
Physical Security Technology Partners
Real-World Breaches
The measures taken to protect physical assets,
such as buildings, equipment and people from unauthorized access, theft, damage, destruction or other threats that originate from the real world.
Access Control
Restrict entry to secure areas, prevent unauthorized access and reduce insider threat risks.
Operational Resilience
Ensure continuity during disruptions through physical safeguards, backup systems and monitoring.
Personnel Safety
Protect staff and visitors from physical harm through surveillance, emergency protocols and controlled access.
Difficulty managing who enters secure areas, especially with shared badges, tailgating or lack of access policies
Fragmented security tools and sensors create blind spots and complicate centralized monitoring and response
Inadequate planning and training hinder effective response to physical threats such as fire, intrusion or disasters
Do you control and monitor access to all sensitive or restricted areas effectively?
Can your facilities withstand and recover quickly from physical disruptions or emergencies?
Do you have clear procedures and tools to detect, report and respond to physical security incidents?
Human Threats
Material Threats
Physical Access Control
Resilience
Worm targeting nuclear centrifuges was designed to spread via USB drives in air-gapped environments
Widespread disruptions occurred after unidentified individuals seemingly breached a data center and were recorded interacting with servers

Risk
Benefits of Risk Management
Common Challenges
Critical Questions
Risk Domains
Risk Technology Partners
Real-World Breaches


The process of identifying, assessing, prioritizing and mitigating potential risks to an organization's assets, operations and reputation.
Risk management involves a systematic approach to identifying and analyzing potential threats, vulnerabilities and impacts, and developing and implementing risk management plans and controls to reduce the likelihood and impact of security breaches.
Proactive Risk Management Continuously identify, assess and mitigate risks, including those introduced by third-party components.
Compliance
Adhere to regulatory and compliance standards, including HIPAA, PCI-DSS and GDPR.
Cyber Insurance
Enable easier access to coverage for legal fees, recovery costs ad business interruption looses related to cyber attacks.
Cloud adoption and third-party relationships have complicated and interwoven IT and business risk
Complex supply chains have forced businesses to account for risk introduced by suppliers and partners
Continuously changing threat landscape and attack surfaces are increasing the likelihood of breaches
Does your risk management program account for business objectives, regulations and risk tolerance?
Are you accounting for the risk introduced by your suppliers and partners?
Do you have cyber insurance and incident response plans to respond and recover from cyber incidents?
Compliance
Cyber Insurance
Risk Governance
Risk Operations
Sensitive data of 560 million customers stolen by breaching a third-party cloud service provider
Third-party systems exploited to steal sensitive data of over 70 million customers
A third-party IT vendor was targeted to steal medical data of 12.9 million individuals


Privacy
Benefits of a Robust Privacy Program
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Real-World Breaches


Implementing policies, procedures and controls
to ensure the protection of personal and sensitive information collected, used and stored by an organization.
Privacy includes the management of
data access, storage and sharing, as well as compliance with privacy regulations such as
GDPR and CCPA.
Enhanced Business Value of PII Increase the value and utility of personal information while effectively managing cyber risk.
Reduced Compliance Burden
Ensure compliance with evolving regulations and reduce risk of fines and legal liabilities.
Protect the Brand
Build effective privacy programs to improve customer confidence and brand reputation.
Non-compliance with complex and evolving regulations such as GDPR, CCPA and HIPAA can lead to severe penalties
Protecting personal data within distributed systems and applications without disrupting business is challenging
Ensuring privacy protections across third-party vendors and supply chains is becoming increasingly complex
Does your privacy program enable business objectives and reduce your risk of non-compliance?
Do you have a breach notification and incident response plan compliant with data privacy regulations?
Do you assess and monitor third-party vendors for privacy compliance?
Privacy Governance
Privacy Operations
Privacy Regulations
Health care data of up to 100 million individuals was compromised due to lack of multi-factor authentication
Private data of 5.5 million individuals exposed due to network authorization flaws
$1.3 billion in fines were issued for violating GDPR international data transfer guidelines





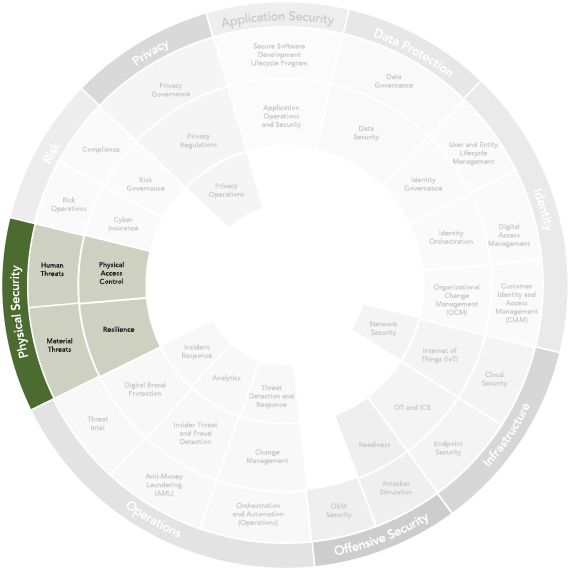







Optiv Market System™
Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop
Trusted By Analysts to Deliver End-to-End Cybersecurity Solutions

Frame Risk Conversations
Arm yourself with risk-based data to have more meaningful conversations with stakeholders.
Monitor Maturity of Domains
Monitor your security program down to individual controls to enable targeted improvements.
Manage and Track Assets
Get a clear snapshot of your portfolio to understand where to invest or consolidate.
Benefits of Optiv Market System™
Optiv Market System™ is a revolutionary reference architecture that provides a holistic view of your cyber coverage to help you identify gaps and compare your investments against peers and competitors.
Use Optiv Market System™ to help you strategically plan your investments, rationalize your technology portfolio and make more informed resourcing decisions.
Speak a Common Language
Establish commonality across your organization to enhance communication.
Improve Flexibility
Dynamically anticipate and adapt to new compliance regulations and new challenges.
Increase Efficiency
Evaluate and optimize your existing tool stack and cyber programs to reduce overhead.



Optiv Named a Leader Overall and Across Services, Innovation and Market
Optiv Named a Leader in IDC MarketScape for Worldwide Cybersecurity Consulting Services
Optiv Named Top Pure-Play Cyber Company in CRN Solution Provider 500 List














































































AppSec Technology Partners
Protect data from unauthorized access, theft, corruption or loss.
Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo

Learn More

Privacy Operations
Benefits of Privacy Operations
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Tactical and day-to-day activities that implement and enforce an organization's privacy governance framework.
It is the practical component of privacy programs, translating governance policies into concrete procedures and technologies.
Improved Operational Efficiency
Eliminates disjointed efforts and provides a clear, reliable workflow for handling privacy tasks.
Scalable Privacy Compliance
Automation enables efficient compliance across multiple regions, products and a growing volume of data. �
Proactive Risk Mitigation
Privacy impact assessments and real-time data monitoring enable proactive risk mitigation.
Regularly changing privacy laws create a complex patchwork of regulations to navigate for global organizations
The rapid adoption of new technologies (like AI and IoT) introduces new privacy governance challenges
Personal data stored in isolated systems managed by different teams makes unified governance difficult
What is your current process for handling data subject access requests (DSARs), such as requests for access or deletion?
What is your current approach to managing third-party vendors who handle your data?
Is "Privacy by Design" incorporated into the development of your new products and services?
Privacy Governance
Privacy Operations
Privacy Regulations
Privacy Policies, Procedures and Standards
Privacy Communications
Privacy by Design Strategy �








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo

Consent Management Systems
Privacy Communications
Data Protection Impact Assessments �

Privacy Governance
Benefits of Privacy Governance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured framework of policies, procedures and controls used to manage and protect personal data throughout its lifecycle.
A strong privacy governance program establishes clear accountability and procedures and ensures that data handling aligns with security policies and privacy laws.
Enhanced Customer Trust
By demonstrating respect for customer data, companies build greater trust, confidence and brand reputation.
Ensures Legal Adherence
Helps comply with complex and
evolving regulations like GDPR and CCPA and avoid fines.
Better Business Outcomes
Ensure data is accurate, consistent and usable, leading to better analytics and business outcomes.
Regularly changing privacy laws create a complex patchwork of regulations to navigate for global organizations
The rapid adoption of new technologies (like AI and IoT) introduces new privacy governance challenges
Personal data stored in isolated systems managed by different teams makes unified governance difficult
What is your current process for handling data subject access requests (DSARs), such as requests for access or deletion?
What is your current approach to managing third-party vendors who handle your data?
Is "Privacy by Design" incorporated into the development of your new products and services?
Privacy Governance
Privacy Operations
Privacy Regulations
Privacy Policies, Procedures and Standards
Privacy Communications
Privacy by Design Strategy �
Consent Management Systems
Privacy Communications
Data Protection Impact Assessments �








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Privacy Regulations
Benefits of Privacy Regulations
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Privacy regulations are laws and legal frameworks that govern how organizations and governments collect, store, manage and use individuals' personal information.
Their primary purpose is to protect individuals' rights by giving them more control over their data, ensuring it is handled responsibly and establishing accountability for data breaches and misuse.�
Avoid Costly Fines and Lawsuits
Compliance reduces the risk of severe penalties of non-compliance with privacy regulations like GDPR and CCPA.
Global Market Readiness
Compliance with international privacy regulations makes it easier to expand into new markets.
Enhanced Security Posture
Privacy regulations often mandate robust security measures that can improve the overall security posture.
Emerging technologies like AI create novel privacy challenges, forcing organizations to adapt their compliance strategies
The landscape of global data privacy laws is constantly changing, making compliance very challenging
Many organizations lack the resources to fund and staff a comprehensive privacy program needed for compliance
What privacy laws and regulations are you currently subject to and what are your privacy compliance concerns?
How do you monitor and respond to changes in privacy regulations?
How do you ensure privacy compliance in AI or third-party vendor data flows?
Privacy Governance
Privacy Operations
Privacy Regulations
Data Subject Rights (DSR) Management
Cross-Border Data Transfer Agreements
Privacy Notices and Consent Mechanisms�
Data Minimization and Retention Policies
Data Protection Impact Assessments
Governance Risk Compliance (GRC) Tool








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Secure Software Development Lifecycle Program �
Benefits of Secure Software Development Lifecycle Program �
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured program to integrate security practices into all phases of software development, from planning and design to coding, testing, deployment and maintenance, ensuring the creation of secure, resilient software by proactively identifying and mitigating security risks.�
Reduced Security Risks
Proactively identify and mitigate vulnerabilities early in development process.�
Cost Efficiency
Mitigating issues early in development cycle is less expensive than after deployment.�
Improved Software Quality
Incorporating security from start enhances software reliability and performance.�
Fixing application security issues discovered in production is costly and disruptive for business
Balancing development velocity, security and regulatory compliance is challenging for development teams
Development teams may not be aware of emerging threats and fail to defend applications against evolving risks�
How do your development teams integrate security practices across all phases of software creation?
How confident are you in your application's ability to withstand emerging cyber threats?
What measures are in place to proactively identify vulnerabilities and compliance issues early in development?
Privacy Governance
Privacy Operations
Privacy Regulations
Application Security Requirements and Design
Component Security Analysis (CSA)
Dynamic Application Security Testing (DAST)
Fuzz Testing
Static Application Security Testing (SAST)
Developer Training �








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Application Operations and Security
Benefits of Application Operations and Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

An integrated approach that combines application development, operations and security practices to ensure applications are built, deployed and maintained securely and efficiently.
It emphasizes collaboration, automation and continuous monitoring from development to runtime operations.
Improved Threat Defense
Integrate security practices into app development and operations to improve resiliency against threats.
Faster Incident Response
Continuous monitoring, automation and collaboration to minimize impact of security incidents.
Cost Savings
Early identification and mitigation of issues reduces development costs and downtime.
Applications and APIs are a leading sources of security incidents, and attacks on AI applications are increasing
Automated AppSec scanners and tools generate false positives and organizations lack actionable insights
Organizations struggle to meet regulatory requirements and to balance development velocity and security
How do you gain visibility into all your APIs, their usage and the regulatory impact of API exposure?
How often do you test AI applications and third-party components and how do you secure them?
How do you incorporate security into your SDLC and monitor applications from development to runtime ?
Privacy Governance
Privacy Operations
Privacy Regulations
Application Detection and Response
Application Discovery and Inventory
Application Vulnerability Management
Application Vulnerability Remediation
Observability
Web and API Application Protection








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Data
Security
Benefits of a Data Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

The practice of protecting digital information from unauthorized access, use, disclosure, disruption, modification or destruction throughout its lifecycle.
It involves implementing policies, technologies and processes to safeguard sensitive data and ensure confidentiality, integrity and availability.�
Protection Against Breaches�Robust security measures like encryption and access controls reduce the risk of data breaches.
Enhanced Customer Trust
Strong data security builds confidence among customers and protects brand reputation.
Business Continuity
Safeguard critical data to prevent business disruptions and ensure regulatory compliance.
Weak access controls allow attackers to exploit sensitive data and cause data breaches
Insider threats may intentionally or unintentionally compromise data
System vulnerabilities and weak encryption may be exploited to expose sensitive information
How confident are you that your current security measures can prevent unauthorized access to sensitive data?
How do you detect and respond to insider threats or accidental data leaks by employees or third parties?
What would be the impact of a data breach on your organization, and how prepared are you to mitigate the risk?
Privacy Governance
Privacy Operations
Privacy Regulations
Access Control
Data Loss Prevention (DLP)
Encryption �
Database Activity Monitoring
Data Obfuscation
Backups and Disaster Recovery








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Data
Governance�
Benefits of a Data Governance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured framework of policies, processes and technologies that ensures data is managed, protected and used effectively across an organization.
It establishes accountability, standards and compliance to maintain data quality, security and accessibility while aligning with business goals and regulations.�
Improved Data Quality
Ensure data is accurate, consistent and reliable for better decision-making.
Increased Data Security
Protect sensitive data through access controls, encryption and monitoring, reducing the risk of breaches.
Enhanced Compliance
Align data practices with laws such as GDPR and CCPA, reducing the risk of legal penalties.
Siloed and fragmented data across departments hinders visibility and usability, reducing operation efficiency
Lack of control over who accesses sensitive data increases breach risks and reputational damage
Varying data practices across teams create inefficiencies and increase risk of non-compliance
How confident are you that your data is accurate, consistent and accessible across departments?
How do you ensure that your data management practices scale with your growth?
How do you prevent unauthorized access to sensitive data and ensure regulatory compliance?
Privacy Governance
Privacy Operations
Privacy Regulations
Data Access Governance
Data Discovery and Classification
Data Lifecycle Management
Data Validation and Cleansing
Metadata Management
Auditing and Monitoring








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Organizational Change Management�
Benefits of Organizational Change Management�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A systematic approach to planning, executing and sustaining changes in security practices, tools or policies across an organization. OCM includes stakeholder engagement, tailored communication plans, comprehensive training programs and post-implementation support to ensure adoption of new technologies, reduce human error and create a security-first culture. This addresses evolving threats while minimizing operational impact. �
Faster Adoption of Tools
Planning and communication reduces employee resistance and ensures smooth adoption of new tools.
Enable Security-First Culture
Stakeholder participation and training helps embed day-to-day security operations.
Reduced Downtime and Costs
Coordinated change helps minimize errors, business disruptions and support costs.
Positioning cybersecurity change as an IT project and not a strategic business imperative can lead to poor adoption
Without cross-functional collaboration, security changes may not align with how people work, leading to friction
Rolling out too many changes at once can overwhelm employees, leading to burnout and decreased engagement
What specific cybersecurity changes have faced pushback, and from which departments?
Are there specific compliance requirements driving your need for OCM?
Do you have a formal change advisory board or governance structure to oversee cybersecurity transitions? �
Privacy Governance
Privacy Operations
Privacy Regulations
Clear Business Strategy and Objectives
Change Management Software/ITSM Tools
Automated Deployment and Rollback Tools
Project Management Discipline
Employee Data and Feedback Mechanism
Secure Communication Platforms








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Identity Governance�
Benefits of Identity Governance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Policies, processes, and tools to oversee the lifecycle of digital identities, ensuring least-privilege access, automated provisioning/deprovisioning and audit trails to meet regulations while reducing insider threats and operational inefficiencies.�
Enhanced Security
Protects against insider and external threats by enforcing least privilege and minimizing the attack surface.
Increased Productivity
Self-service portals and automated user lifecycle management ensure timely access to resources.
Simplified Compliance
Clear, documented and centralized record of access rights helps prove regulatory compliance.
Integrating a new governance platform with complex hybrid and multi-cloud environments is difficult
Legacy tools were not built to govern non-human identities, creating significant blind spots
Poor user-experience and overly complex governance workflows can lead to user resistance and poor adoption
What are the biggest pain points in your current process to onboard and offboard employees?
How does your organization handle non-human identities, such as service accounts and bot accounts?
How do you currently conduct access reviews and enforce segregation of duties policies?
Privacy Governance
Privacy Operations
Privacy Regulations
Identity Data Governance
Identity Directory Data
Know Your Customer (KYC)�
Identity Analytics
Authoritative Source of Identity Data
Identity Correlation Keys








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Identity Orchestration�
Benefits of Identity Orchestration
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Identity Orchestration automates and abstracts identity workflows across complex IT environments, integrating multiple identity providers to enforce unified policies, seamless authentication, risk management and compliance.
It acts as an intelligent control plane that coordinates identity flows in real-time, enforcing consistent policies across multiple systems. �
Stronger Security Posture �Reduce the risk of unauthorized access and data breaches, by enforcing consistent security policies across complex systems.�
Frictionless User Journeys
Streamline user authentication and authorization processes, creating a seamless user experience.
Faster M&A Integration
Provides a vendor-agnostic approach that simplifies combining different identity infrastructures.
Connecting legacy applications that lack modern APIs to orchestration platform can be complex and costly
Orchestrating a seamless user-experience across fragmented identity stack can be a major technical challenge
The proliferation of non-human identities, can make orchestration and oversight overly complex
How do you manage authentication policies across your hybrid or multi-cloud environment?
What are the pain points, business drivers and key objectives for exploring identity orchestration?
What integrations with third-party applications are critical for your business?�
Privacy Governance
Privacy Operations
Privacy Regulations
Identity Workflows and User Journeys
Identity Orchestration and Automation �
Centralized Policy Definitions
Identity Providers and Directories








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Customer Identity and Access Management (CIAM)�
Benefits of Customer Identity and Access Management�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

CIAM encompasses technologies and processes for handling customer authentication, authorization and profile management across apps and channels, including registration, login, consent handling and fraud prevention, while ensuring seamless user experience and compliance with privacy laws. �
Enhanced Customer Trust
By demonstrating respect for customer data, companies build greater trust, confidence and brand reputation.
Ensures Legal Adherence
Helps comply with complex and
evolving regulations like GDPR and CCPA and avoid fines.
Better Business Outcomes
Ensure data is accurate, consistent, and usable, leading to better analytics and business outcomes.
Regularly changing privacy laws create a complex patchwork of regulations to navigate for global organizations
The rapid adoption of new technologies (like AI and IoT) introduces new privacy governance challenges
Personal data stored in isolated systems managed by different teams, makes unified governance difficult
What is your current process for handling data subject access requests (DSARs), such as requests for access or deletion?
What is your current approach to managing third-party vendors who handle your data?
Is "Privacy by Design" incorporated into the development of your new products and services?
Privacy Governance
Privacy Operations
Privacy Regulations
Privacy Policies, Procedures and Standards
Privacy Communications
Privacy by Design Strategy �
Consent Management Systems
Privacy Communications
Data Protection Impact Assessments �








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Digital Access Management
Benefits of Digital Access Management�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Use of centralized systems to control, monitor and audit access to digital files, media, and resources across networks, often using role-based permissions, encryption and audit trails to prevent misuse of licensed content and data leaks, enforce compliance and streamline sharing and collaboration across teams. �
Mitigate Legal Risks
Enforce copyright and usage rights for assets by tracking licenses, minimizing legal risks and fines.
Secure Sharing
Share assets with external partners securely eliminating risk of data breaches though insecure transfers.
Reinforced Brand Identity
Centralized hub for approved, on-brand assets, prevents usage of using incorrect or outdated versions.
Migrating millions of digital assets from old, decentralized storage into a new DAM system is a huge undertaking
Moving from uncontrolled workflows to a formal, governed DAM process is often a major shift for creative teams
An improperly scoped DAM system can face scalability issues as number of assets and usage increase in future
What are your primary business goals for implementing Digital Access Management?
What are your current policies for managing asset rights, licenses and usage permissions?
How do you see your digital asset needs evolving in the next 3 to 5 years?
Privacy Governance
Privacy Operations
Privacy Regulations
Privileged Access Management (PAM)
Dynamic Secrets
Password Management
Sefl-Service Password Management
Directory Services and Authorization
Single Sign-On and Federation








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


User and Entity Lifecycle Management�
Benefits of User and Entity Lifecycle Management
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A systematic approach for overseeing the complete digital lifecycle of all identities, both human and non-human, within a company's digital infrastructure.
This process manages every phase of an identity's existence, from its first creation to its final retirement, to ensure access privileges are consistently aligned with a company's policies and compliance requirements.�
Mitigated Insider Threats
Prompt and automated deprovisioning upon departure or role change reduces the risk of malicious insiders.
Reduced IT costs
With automated workflows, help desk tickets related to access and passwords decrease significantly.
Simplified Audits
Automated audit trail of who has access to what, when and why, simplifies the process of demonstrating compliance.�
Inaccurate or incomplete identity data can lead to errors in automated workflows and inaccurate provisioning
Integrating legacy systems into modern identity protocols and workflows is often difficult and requires custom work
Lack of a shared vision and collaboration across HR, legal and business units can lead to inefficient workflows
How do you detect and handle orphaned accounts or over-privileged roles?
Do you have real-time auditing for non-human entities like service accounts or IoT devices?
What specific compliance requirements (e.g., GDPR, SOX) are you addressing with lifecycle management?
Privacy Governance
Privacy Operations
Privacy Regulations
Identity Auditing and Reporting
Entitlement Management
Role/Attribute Based Access Control
Segregation of Duties
Service Account Administration
User Lifecycle Management (Joiner Mover Leaver)








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Internet of Things
Benefits of IoT Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Internet of Things (IoT) Security protects interconnected devices (e.g., smart sensors, medical devices, industrial sensors) from vulnerabilities like weak authentication or unpatched firmware.
It includes device discovery, network segmentation, encryption and anomaly detection to prevent botnets, data breaches or operational disruptions�
Enhanced Uptime and Reliability
A secure IoT infrastructure results in stable, consistent performance and less downtime for critical systems.
Creation of Safer Environments
Protect against malfunctions and cyberattacks that can endanger employees or patients.
Reduced Financial Liability
IoT devices are common entry points for attackers. Robust IoT security can prevent costly breaches and IP theft.
Many IoT devices have limited computational resources, preventing them from running robust security tools
IoT market is highly fragmented, with countless vendors and insufficient security standards, complicating security
Businesses often lack the specialized security expertise to implement and manage robust IoT security solutions
How many IoT devices are currently connected to your network, and are they inventoried?
What’s your process for updating firmware, and how often are devices left unpatched?
What network segmentation strategies do you use to isolate IoT from IT infrastructure?
Privacy Governance
Privacy Operations
Privacy Regulations
Asset Inventory and Visibility
Vendor Accountability and Transparency
Network Segmentation
Secure Firmware and Software Updates
Device Authentication
Security Monitoring and Incident Response�








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Cloud
Security
Benefits of Cloud Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A set of technologies, policies, controls, and services used to protect data, applications and infrastructure hosted in cloud computing environments, where security responsibility is divided between the cloud service provider (CSP) and the customer.
It focuses on the unique risks and challenges of cloud environments, including public, private and hybrid clouds. �
Reduced and Predictable Costs
Cloud security solutions reduce the need for investment in hardware and provide usage-based operational cost models.
Scalability and Flexibility
Scale on demand, protecting assets and users as the business grows.
Advanced Threat Detection
CSPs invest heavily in cutting-edge security tech, including AI, for real-time threat detection.
A shortage of skilled cloud security professionals is a major challenge for many companies
Employees using unauthorized cloud services and apps can introduce significant security risks
Use of multiple cloud providers and hybrid infrastructure creates operational complexity and security controls
What tools do you use for security visibility across multi-cloud or hybrid environments, and where are the gaps?
What specific cloud misconfigurations, risks or threats are you concerned about?
What training or skill gaps exist in your team for managing cloud-native security tools?
Privacy Governance
Privacy Operations
Privacy Regulations
Cloud Security Posture Management (CSPM)
Cloud Workload Protection Platform (CWPP)
Cloud Native App Protection Platform (CNAPP)
Container Security
SaaS Security Posture Management (SSPM)
Secure Cloud Migration Services








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Endpoint Security�
Benefits of Endpoint Security�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Cybersecurity practice that protects network-connected devices or endpoints, like laptops, desktops and mobile devices, from cyber threats.
It uses real-time monitoring, behavioral analytics and automated response to detect, prevent and respond to attacks that could originate from these devices, leading to exploitation of an organization's network. �
Secure Remote Access
Ensure devices are secure regardless of location, enforcing consistent security policies for all remote workforce.
Rapid Security Response
Automatically isolate compromised devices and terminate malicious processes, drastically reducing risk.
Centralized Management
Management and monitoring from a single console improves visibility and enables quick threat response.
Diversity of devices and software makes it hard to enforce consistent security policies across all endpoints
Alerts and false positives from a large number of endpoints can overwhelm security teams
Businesses often lack the budget, staff, and expertise required to implement and manage endpoint security solutions
How do you manage alert fatigue from endpoint security tools, and what’s your false positive rate?
What specific risks have you faced with BYOD or remote work devices in the past year?
How integrated is your endpoint security with your SIEM or SOC workflows?
Privacy Governance
Privacy Operations
Privacy Regulations
Endpoint Protection Platform (EPP/EPS)
Enterprise Browser
Firmware Security
Host-based Intrusion Detection and Prevention
Host Integrity Monitoring
Mobile Device Management (MDM)








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


OT and
ICS�
Benefits of OT and ICS Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Operational Technology (OT) and Industrial Control Systems (ICS) support critical infrastructure sectors such as energy, manufacturing and utilities.
They ensure the safety, availability and integrity of operations, and help prevent breaches that could lead to catastrophic physical consequences, including equipment damage, environmental disasters or loss of life.
Minimize Physical Safety Risks
Prevent malicious actors from causing safety incidents, equipment damage or environmental hazards.
Ensure Operational Uptime
Minimizes operational disruptions and unplanned downtime, which can lead to significant financial losses.
Enable IT-OT Convergence
As organizations connect OT systems to their IT networks, OT security helps manage the expanded attack surface.
Many OT and ICS systems run on outdated operating systems and devices that were not built to enable security
Because OT systems prioritize continuous operation, applying security patches can be highly disruptive
IT/OT convergence expands the attack surface, creating vulnerabilities in IT that can be exploited to pivot into critical OT systems
Do you have a complete and up-to-date inventory of all OT/ICS assets, including proprietary devices?
How do you secure OT devices that cannot be patched or updated?
What are the applicable regulatory requirements for your industry, and how do you ensure compliance?�
Privacy Governance
Privacy Operations
Privacy Regulations
Asset Inventory and Visibility
Access Control and Physical Security
Vulnerability and Patch Management
Supervisory Control and Data Acquisition (SCADA) security
Industrial Control Machinery (ICM) security
Configuration Management and Disaster Recovery








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Network
Security
Benefits of Network Security
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Network security is the practice of protecting a computer network and its data from cyber threats and unauthorized use.
It involves a combination of hardware, software, and processes to prevent, detect and mitigate attacks, ensuring the network's confidentiality, integrity and availability. �
Enhanced Customer Trust
By safeguarding critical data, businesses can build and maintain customer trust and brand reputation
Ensure Business Continuity
Minimize disruptions by mitigating threats such as DDoS attacks and malware.
Support Digital Transformation
Enables safe business innovation and cloud expansion by using strategies like Zero Trust.
Maintaining consistent network security policies is difficult for companies with multi-cloud and hybrid environments
Detecting insider threats can be challenging since they come from within the network
Despite network security controls, human error and social engineering continues to be a leading source of breaches
How do you secure data across hybrid or mutli-cloud networks?
What’s the efficacy of your current firewall rules, and when were they last audited?
What are the biggest network security risks you are concerned about and how do you currently monitor for those?
Privacy Governance
Privacy Operations
Privacy Regulations
API Gateway Security Controls
DDoS Mitigation/Protection
Firewall/UTM/NGFW
Secure Access Service Edge (SASE)
Secure Web Gateway
Network Access Control (NAC)








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Readiness
Benefits of Readiness
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Readiness refers to an organization’s preparedness to proactively test, detect and respond to cyber threats by leveraging offensive security techniques, such as penetration testing, red teaming and vulnerability assessments.
It involves maintaining a robust security posture through continuous evaluation, training and process optimization to anticipate and counter real-world attacks effectively.�
Improved Resilience
Continuous readiness keeps defenses aligned with evolving threats, ensuring adaptability and resilience.
Strengthened Incident Response
Regular offensive testing hones detection and response capabilities for quick mitigation of attacks.
Improved Security Awareness
Ongoing simulation and training fosters a security-first culture to recognize and address threats.
Untested or outdated incident response plans can fail under real attacks
Over-reliance on automated defenses may cause teams to miss sophisticated attacks
Failure to demonstrate proactive security testing can lead to regulatory non-compliance and penalties
When was the last time your incident response plan was tested against realistic attacks, and how effective was it?
How are you ensuring your employees are prepared to recognize and avoid social engineering attacks like phishing?
How confident are you that your organization can mitigate a sophisticated attack before it causes significant damage?�
Privacy Governance
Privacy Operations
Privacy Regulations
Incident Response Plans
Business Continuity and Disaster Recovery Plans
Tabletop Exercises and Simulations
Security Awareness Training
Detection and Response Capabilities
Physical Security Testing (Readiness)








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Attacker
Simulation
Benefits of Attacker Simulation
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

The practice of mimicking real-world cyberattacks to test an organization’s defenses, identify vulnerabilities and improve security posture.
It involves controlled, ethical hacking techniques to simulate adversary tactics, techniques and procedures (TTPs) across systems, networks and applications.
Proactive Vulnerability ID
Uncover weaknesses in systems, application and processes before malicious actors exploit them.
Improved Incident Response
Test and refine your ability to detect, respond to and mitigate attacks.
Enhanced Security Awareness
Educate teams about emerging threats and foster a security-first mindset through practical exposure.
Organizations often lack visibility into exploitable weaknesses, and theoretical security measures may fail in practice
Due to overreliance on automated tools, security teams can miss sophisticated threats and attacks
Slow or ineffective incident response can increase damage caused by attacks
How confident are you that your defenses can withstand a sophisticated cyberattack from a determined adversary?
What processes do you have in place to identify and test vulnerabilities that automated tools might miss?
How do you meet regulatory requirements for proactive security testing and demonstrate due diligence to auditors?
Privacy Governance
Privacy Operations
Privacy Regulations
Control Testing and Validation
Penetration Testing
Purple Teaming
Rules of Engagement
Notification and Escalation Routes
Post-Exercise Debriefing









Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


OEM
Security
Benefits of OEM Security�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Practices, technologies, and processes implemented by Original Equipment Manufacturers (OEMs) to embed security features into hardware, software and firmware during the production of components or systems.
This includes secure boot mechanisms, encryption, access controls and threat-resistant designs to protect integrated products from cyber threats.�
Enhanced Product Quality
Embedding security at the hardware level strengthens overall product resilience and reliability.
Faster Time-to-Market
Secure-by-design approach streamlines and accelerates production without compromising safety.�
On-going Protection
Regular updates from OEMs keep products secure against evolving threats and ensure compliance.
Integrated systems are often exposed to supply chain vulnerabilities that are hard to mitigate for end-users
Applying security updates to sensitive IoT and OT devices and integrated systems can be very challenging
Cyber Threats are constantly evolving, and organizations often lack expertise to detect and mitigate risks
How are you embedding security into your hardware and firmware to prevent supply chain vulnerabilities?
How scalable are your security practices across the product lifecycle, from design to end-of-life data disposal?
How confident are you in protecting against firmware attacks or unauthorized modifications in your products?
Privacy Governance
Privacy Operations
Privacy Regulations
Supply Chain Risk Management
Secure Default Configurations
Open-Source Intel (OEM Security)
Product End-of-Life Policy
Authentication and Authorization
Compliance with Standards and Regulations








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Anti-Money Laundering
Benefits of Anti-Money Laundering
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Integration of cybersecurity measures, financial monitoring, data analysis, regulations and procedures to detect, prevent and report financial crimes linked to money laundering, financing of illegal activities and cyber-enabled fraud. �
Proactive Defense
Detect and prevent costly financial cybercrimes by adapting to new laundering tactics.
Financial Data Integrity
Ensure confidentiality and integrity of financial data against internal and external threats.
Regulatory Compliance
Ensure compliance with evolving AML regulations and reduce the risk of expensive fines.
Keeping up with global AML regulations and balancing robust monitoring with privacy laws can be challenging
Integrating AML systems with cybersecurity and legacy banking platforms can be very complex
High false positive rates in transaction monitoring can overwhelm compliance teams
What challenges do you face integrating AML tools with your cybersecurity stack or core banking systems?
How do you stay ahead of emerging laundering tactics, such as those involving cryptocurrencies or AI-driven fraud?
Which financial regulations (e.g., BSA, FATF, AMLD) are critical for your org and how do you ensure compliance?
Privacy Governance
Privacy Operations
Privacy Regulations
Transaction Monitoring
Suspicious Activity and Transaction Reporting
Know Your Customer (KYC)
Sanctions Screening
Audit and Compliance Testing
Record Keeping and Data Retention�








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Change Management�
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured methodology for planning, implementing, and monitoring changes to IT systems, such as software updates, configuration adjustments or infrastructure upgrades, to minimize security risks.
It involves risk assessments, approval workflows and testing to ensure changes don’t introduce vulnerabilities, disrupt operations or weaken compliance.�
Minimize Service Outage
Carefully planned and tested system updates minimize business disruptions.
Reduced Risk
Reduce the risk of introducing new vulnerabilities during system updates.
Faster Recovery
If issues arise, detailed backup and rollback plans allow for quick and effective recovery.
Balancing rapid deployment of updates (e.g., zero-day patches) with thorough security testing creates tension
Staff may resist adoption of secure practices due to unfamiliarity, fear of disruption or lack of training
Lack of comprehensive monitoring makes it hard to track change impacts across complex environments, increasing risk
How do you assess the security impact of changes, particularly for high-risk and urgent software patches?
What tools or processes do you use to automate change testing, validation and rollback in case of failures?
What metrics do you use to evaluate the effectiveness of your change management process?
Privacy Governance
Privacy Operations
Privacy Regulations
Configuration Management and ITSM Tools
Inventory (Asset) Management
Risk and Impact Assessment
Vulnerabiity and Patch Management
Change Approval Board and Rollback Plans
Automated Version Control, Deployment and Rollback Tools








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Orchestration and Automation�
Benefits of Orchestration and Automation
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured approach for streamlining security operations by integrating tools, automating repetitive tasks and orchestrating workflows for threat detection, response and remediation.
It reduces manual effort in processes like alert triage, incident response and compliance reporting, enabling scalable operations across complex, hybrid environments.�
Improved Efficiency and Focus
Automation of repetitive time-consuming tasks frees up security teams to focus on strategic threats.
Accelerated Response
Automated playbooks can execute response actions and reduce the mean time to detect and respond.
Continuous Compliance
Monitoring for policy violations simplifies auditing and adherence to regulatory requirements.�
Integration of SOAR platforms with legacy or heterogeneous tools often faces compatibility issues
Configuring and maintaining orchestration rules requires specialized expertise, which many organizations lack
Excessive reliance on automation without human oversight can lead to errors and disrupt business operations�
What manual tasks in your SOC consume the most time, and how could automation address them?
What integration and orchestration challenges do you face with the security tools in your stack (e.g., SIEM, EDR, firewalls)?
How do you measure ROI for automation, such as reduced analyst workload or faster MTTR?
Privacy Governance
Privacy Operations
Privacy Regulations
Security Orchestration Automation and Response
DevSecOps
Technology Automation and Orchestration
Business Automation and Orchestration
Continuous Security Validation
Robotics Process Automation








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Threat
Intel
Benefits of Threat Intel
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Collecting, analyzing, and disseminating evidence-based knowledge about adversaries’ tactics, techniques, and procedures (TTPs) from sources like open-source feeds, dark web monitoring or industry sharing.
It guides proactive defenses and security decisions by providing context on threat actors, vulnerabilities and indicators of compromise.
Improved Risk Management
Contextualized data helps prioritize genuine threats and reduce false positives.
Enhanced Decision-Making
Organizations can use industry-specific threat intel to make sound security investments.
Reduced Costs
Early threat warnings enable proactive mitigation, reducing financial impact of attacks.
Analyzing vast amounts of threat data to identify actionable intelligence is time-consuming and resource-intensive
Incorporating threat intel across multiple systems such as SIEM, EDR or SOAR is challenging and limits usability
Keeping intelligence current amidst fast-changing TTPs is hard and requires frequent updates and analysis
Which threat actors or TTPs are most relevant to your industry and how are you tracking them?
How do you disseminate threat intelligence across your security team and other stakeholders?
What metrics do you use to evaluate the value of your threat intelligence program?
Privacy Governance
Privacy Operations
Privacy Regulations
Threat Intelligence Platform
Threat Intelligence Program Development
Disinformation Detection
IR Attribution
Threat Actor Tracking and Reporting
VIP Monitoring








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Insider Threat and Fraud Detection�
Benefits of Insider Threat and Fraud Detection
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Insider threat and fraud detection focuses on identifying and mitigating risks from internal actors— employees, contractors or partners — whether malicious or negligent. It uses monitoring, behavior analysis and data loss prevention tools to detect and stop anomalous actions. �
Prevent Insider-Driven Breaches
Reduce data loss from fraud or unauthorized access by internal actor.
Minimize Financial Loss
Identify malicious or compromised insiders early to prevent business disruptions.
Reduce Remediation Costs
Early detection reduces the time and cost of responding to and recovering from a major breach.
Monitoring employee behavior risks violating privacy laws or eroding trust, requiring careful policy design
Normal variations in user behavior can trigger false alerts and overwhelm analysts and systems
Correlating insider threat data across disparate systems is challenging, often leading to incomplete risk profiles
What specific insider behaviors are your top concerns, and how are you monitoring them?
What privacy regulations shape your monitoring policies, and how do you balance compliance with employee trust?
How do you integrate insider threat data with fraud detection or broader cybersecurity systems, and what gaps exist?
Privacy Governance
Privacy Operations
Privacy Regulations
User Behavior Analytics
Data Loss Prevention
Privileged Access Management
Separation of Duties
Access Review and Least-Privilege Enforcement
Monitoring and Alerting








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Digital Brand Protection�
Benefits of Digital Brand Protection
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Leverage monitoring, threat intelligence and takedown services to safeguard an organization’s online reputation, trademarks and digital assets from threats like phishing, counterfeiting, domain squatting and impersonation.
It uses automated tools to detect and mitigate risks across social media, e-commerce, mobile apps and dark web to protect customer trust and financial performance.�
Preserve Brand Value
Prevent unauthorized use of brand that can dilute reputation and value of intellectual property.
Minimize Financial Loss
Proactively detect and remove counterfeit products from e-commerce sites.
Protect Customer Trust
Ensure customers are not tricked into buying counterfeit goods or falling victim to phishing scams.
Sophisticated tactics like AI-generated deepfakes or dynamic phishing sites evolve faster than detection systems
The volume of online mentions, especially across social media and dark web channels, can overwhelm teams
Taking down malicious content across global jurisdictions with different legal frameworks is complicated
How do you currently stop impersonation or counterfeiting incidents and what are the response time bottlenecks?
Which digital channels pose the greatest risk to your brand and how are you monitoring them?
How well do your brand protection efforts integrate with existing threat intelligence or cybersecurity workflows?
Privacy Governance
Privacy Operations
Privacy Regulations
Continuous Monitoring and Scanning
Takedown and Enforcement Procedures
Source Code Leak Detection
Domain Management and Protection
Anti-Counterfeiting and Serialization
Legal Strategy for Intellectual Property Management








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Threat Detection and Response�
Benefits of Threat Detection and Response
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

TDR encompasses proactive identification, investigation and mitigation of cyber threats across endpoints, networks and cloud environments using tools like EDR, XDR and threat hunting. It combines real-time monitoring, behavioral analytics, threat intel and rapid response to minimize impact of cyberattacks. �
Faster Threat Response
Continuous monitoring to detect and respond to threats in their earliest stages, reducing damage.
Reduced Business Disruption
By rapidly containing threats, TDR minimizes operational downtime.
Neutralize Complex Threats
Threat hunting and advanced analytics enable you to stop threats that evade traditional defenses.�
High volumes of alerts and false positives overwhelm analysts, delaying response to critical threats
Advanced threat hunting and response require specialized expertise, which many organizations lack
Many threat response workflows still lack sufficient automation, which slows down the response time
What are your biggest gaps in detecting threats across endpoints, networks or cloud environments?
What threat hunting capabilities do you currently have and what advanced threats are you struggling to detect?
How well does your detection system integrate with response automation or threat intelligence platforms?
Privacy Governance
Privacy Operations
Privacy Regulations
Extended Detection and Response (XDR)
SIEM and Log Management
Detection Engineering
Threat Intelligence
Security Orchestration, Automation and Response (SOAR)
Incident Response Plan Activation








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Analytics
Benefits of Analytics
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

The systematic use of data collection, processing, visualization and analysis techniques to uncover hidden threats and vulnerabilities.
It often employs dynamic and advanced methods like machine learning, artificial intelligence (AI) and behavioral analysis to proactively identify anomalies and patterns that indicate malicious activity.�
Data-Driven Risk Assessment
Better risk Identification and prioritization based on historical and real-time data analysis.
Improved Incident Response
Correlate disparate events to provide rich context and accelerate incident response.
Proactive Threat Detection
Threat data and behavior analysis can uncover unknown and insider threats that other tools can miss.
It is difficult to get actionable insights due to massive amount of data and alerts produced by modern networks
Alert fatigue and false positives can lead to delayed responses, burnout and critical threats being missed
Without analytics and automation, security teams can miss unknown zero-day exploits and insider threats
How are you currently handling the volume and complexity of security alerts? Is alert fatigue a concern?
How does your current solution protect against new and emerging threats, not just known ones?
Can you quantify the ROI of your analytics investment, such as reduction in mean time to detect or respond?
Privacy Governance
Privacy Operations
Privacy Regulations
Security Information Event Management (SIEM)
User and Entity Behavior Analytics (EUBA/UEBA/UBA)
Network Flow Analysis
Blockchain Analytics
Machine Learning/AI
Natural Language Processing (NLP)









Incident Response�
Benefits of Incident Response
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A disciplined process for identifying, containing, eradicating, and recovering from cybersecurity incidents, such as data breaches, ransomware or DDoS attacks.
IR often uses playbooks, technology and cross-functional coordination to minimize damage, restore operations and prevent recurrence.�
Reduced Recovery Costs
Contain breaches faster, minimizing legal fees, regulatory fines and data recovery costs.
Minimize Financial Loss
By minimizing downtime, effective incident response can prevent severe financial and reputational losses.
Lower Insurance Premiums
Insurers reward companies with a strong IR plan, viewing them as lower risk.
Overreliance on manual workflows slows response times during large-scale attacks, increasing damage potential
Limited staff, experience, budget or tools during major incidents can hinder effective response
Failing to integrate lessons learned from incidents into future preparedness risks repeated vulnerabilities
How frequently do you test and update your incident response playbooks, and what scenarios do they cover?
What training or simulation programs do you have to prepare for evolving threats like zero-day exploits?
What integrations with tools like SIEM, EDR or SOAR are critical for streamlining your incident response process?
Privacy Governance
Privacy Operations
Privacy Regulations
Incident Response Plan Validation
Triage and Prioritization
Containment and Isolation
Incident Management Coordination
Case Management
Forensics and eDiscovery








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Material Threats
Benefits of Mitigating Material Threats
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Material Threats involve physical or supply chain risks, such as tampered hardware, unpatched firmware or compromised components, that can lead to data breaches, operational failures and safety risks.
Maintain Business Continuity
Minimize disruptions caused by material physical threats, such as sabotage or theft.
Lower Insurance Costs
Comprehensive physical security can make your organization a lower-risk candidate for insurance.
Safeguard Critical Services
Prevent disruption of services like power, water, and transportation essential for public safety and economic stability. �
The complexity of global supply chains makes it difficult to trace the complete lineage of all components in a product
Many organizations lack the expertise to perform forensic analysis on firmware or hardware to detect tampering
Older devices may no longer receive security updates, leaving them exposed to exploitation
What do you consider to be your most significant physical material threats?
What visibility do you have into your vendor supply chains and how do you detect counterfeit or tampered goods?
How do you verify the integrity and origin of firmware updates?
Privacy Governance
Privacy Operations
Privacy Regulations
Inventory and Asset Management
Controlled Access
Environment Monitoring and Surveillance
Configuration Management Database
Risk Assessments and Threat Modeling
Supply Chain Risk Management








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Resilience
Benefits of Resilience
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Cyber Resilience integrates prevention, detection, response and recovery to ensure organizations can withstand and recover from cyber incidents, maintain operations during crises and learn from incidents to strengthen defenses.�
Faster Disaster Recovery
Resilient organizations regularly test their emergency response to ensure quicker recovery from disasters.
Reduced Long-Term Costs
Investing in resilience can reduce losses from incidents, remediation costs and insurance premiums.
Enable Confident Innovation
A clear resilience protocol can empower organizations to pursue disruptive innovation and agility.
Organizational silos between physical security and other teams can prevent a unified, holistic response to threats
The rise of new physical threats, such as drone-based intrusions and AI tactics, requires constant adaptation
Failure to test and maintain plans can cause confusion and delays in recovering from real security incidents
What are your most critical physical assets and operations that must be protected?
Do you have an incident response plan for physical security events, and when was it last tested?
How do future expansion plans or business changes affect your physical security posture?
Privacy Governance
Privacy Operations
Privacy Regulations
Business Continuity and Disaster Recovery Plans
Incident Response Plan
Supply System (Utilities) Security
Backups and Data Redundancy
Network Segmentation and Isolation
Decentralized Systems/Cloud Agility








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Human
Threats
Benefits of Mitigating Human Threats
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Actions, errors, or negligence of individuals that create or exploit vulnerabilities in an organization's physical defenses to facilitate a cyberattack.
This encompasses both external attackers manipulating people to gain physical access and internal personnel who misuse their privileges or make mistakes.
Minimize Financial Loss
Human error is a major cause of data breaches. By preventing it, companies avoid financial and reputational losses.
Ensure Human Safety
Avoid OT/ICS equipment malfunction or service disruptions that can endanger human life.
Maintain Uptime
Prevent operational disruptions by stopping the human actions that can lead to physical breaches.
Many security training programs focus on digital threats, with insufficient emphasis on physical security procedures
Over-privileged or unmonitored access to sensitive areas for third-party vendors is a major risk
Overly restrictive or inconvenient security measures can frustrate employees and encourage workarounds
How do you verify that your existing physical security controls are effective in deterring intruders?
Have you conducted any social engineering or physical penetration tests, and what were the results?
What are the most significant business impacts you would face from a security incident that starts with an employee?
Privacy Governance
Privacy Operations
Privacy Regulations
Physical Least Privilege
Physical Policies and Procedures
Physical Security Training
User Behavior Analytics
Termination Procedures
Background Checks and Vetting








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Physical Access Control
Benefits of Physical Access Control
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

The security measures and systems used to restrict, monitor, and manage who can enter or exit sensitive areas like data centers, offices or manufacturing floors.
Unlike logical access controls, which govern digital assets like data and applications, physical access controls are concerned with securing tangible spaces and assets from unauthorized access.
Prevent Unauthorized Access
Deter intruders and malicious insiders by ensuring only authorized personnel can access secure areas.
Protect Intellectual Property
By securing labs, server rooms, and R&D facilities, organizations can prevent theft, vandalism and corporate espionage.
Increase Efficiency
Modern access controls offer a frictionless experience, without the hassle of physical keys or cumbersome sign-in processes.�
Attackers can use social engineering tactics to trick people into granting them physical access
In remote work environments, organizations now have to protect assets outside the traditional office perimeter
Finding the right balance between a secure environment and an efficient user-workflow is a constant challenge
What would a more secure and efficient access control process mean for your business?
How do you manage visitors, and what is your current workflow to handling physical security incidents?
How critical is it to have real-time monitoring and reporting capabilities?
Privacy Governance
Privacy Operations
Privacy Regulations
Access Control Systems
Surveillance Systems
Alarm Systems and Sensors
Visitor Management Systems
Physical Barriers and Deterrents
Policies and Security Zones








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Compliance
Benefits of Compliance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Process of ensuring an organization adheres to relevant laws, regulations, standards and internal policies governing data protection, privacy and security.
It involves implementing controls, audits, and processes to meet requirements such as GDPR, HIPAA, PCI-DSS, or ISO 27001, mitigating legal, financial and reputational risks.
Avoidance of Penalties
By demonstrating respect for customer data, companies build greater trust, confidence and brand reputation.
Market Access
Enable businesses to operate in regulated industries and regions, opening new opportunities.
Enhanced Security
Compliance mandates robust security controls, improving security posture and trust with customers.
Navigating complex and evolving regulations like GDPR or CCPA is challenging
Inconsistent policy enforcement across teams can create non-compliance and security risks
Inadequate controls or documentation can result in failed audits and data privacy risks
What challenges do you face in keeping up with evolving regulations and ensuring adequate controls over time?
How confident are you that your organization fully complies with regulations like GDPR or PCI-DSS?
How would a regulatory violation impact your reputation and customer trust, and can you mitigate those risks?
Privacy Governance
Privacy Operations
Privacy Regulations
Industry and Regulatory Compliance Objectives
Compliance Assessment Tools
Auditing and Monitoring Tools
Data Classification and Handling
Policy Management and Enforcement
Risk Management Framework








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Risk Operations
Benefits of Risk Operations
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

The operational processes, tools, and activities used to actively manage, monitor and mitigate risks within an organization, particularly those related to cybersecurity, compliance and business continuity.
It involves real-time risk assessment, incident response, and continuous monitoring to ensure risks are identified and addressed promptly to protect organizational assets and operations.
Real-time Risk Mitigation
Enables rapid identification and response to threats, minimizing the impact of cyber incidents.
Cost Efficiency
Reduces financial losses by addressing risks before they escalate into costly breaches.
Improve Situational Awareness
Improved decision-making by continuous monitoring of risk landscape and compliance posture.
Slow identification, prioritization and mitigation of risks can lead to significant business impact
Ineffective or uncoordinated workflows and risk responses across teams can worsen incident outcomes
Failure to incorporate compliance checks into risk management can increase the risk of non-compliance
How quickly can your organization detect and respond to a cyber risk before it escalates into a major incident?
What would be the operational and financial impact of a prolonged system outage or data breach?
How do you ensure regulatory compliance in your day-to-day operations, and are those processes scalable?
Privacy Governance
Privacy Operations
Privacy Regulations
Risk Assessment, Reporting and Communication Plan
Governance Risk Compliance (GRC) Tool
Key Risk Indicators (KRIs) Monitoring
Control Testing and Validation
Cyber Security Awareness Training
Monitoring of External Threats and Third-Party Risk








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Cyber Insurance
Benefits of Cyber Insurance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

Cyber Insurance is a specialized insurance policy designed to protect organizations from financial losses and liabilities resulting from cyber incidents, such as data breaches, ransomware or system disruptions.
It typically covers costs like legal fees, ransom payments, data recovery and reputational damage mitigation, while also supporting risk management and compliance efforts.
Financial Protection
Reduces costs associated with cyber incidents, including legal fees, fines and recovery expenses.
Incident Response Support
Provides access to expert resources to mitigate breaches and recover reputation.
Business Continuity
Funds recovery efforts, ensuring operations resume quickly after an incident.
Cyber incidents can incur massive costs, including legal and recovery expenses
Cyber Incidents can damage an organization’s reputation and trust with customers
Ransomware attacks are increasingly demanding costly payments and recovery efforts
What would be the total financial and legal impact of a cyber breach on your organization?
Are you confident your organization can absorb the cost of a cyber incident without insurance coverage?
Do you have the resources and expertise to manage a complex cyber incident, such as a ransomware attack?
Privacy Governance
Privacy Operations
Privacy Regulations
Multi-Factor Authentication (MFA)
Endpoint Detection and Response (EDR)
Incident Response Plan and Testing
Employee Security Awareness Training
Vulnerability and Patch Management
Accurate Disclosure of Risk Posture








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo


Risk Governance
Benefits of Risk Governance
Common Challenges
Critical Questions
Privacy Domains
Privacy Technology Partners
Key Dependencies/Security Controls

A structured framework of policies, processes, and oversight mechanisms designed to identify, assess, manage and monitor risks across an organization, particularly those related to cybersecurity, compliance and operations.
It ensures risks are aligned with business objectives, prioritized effectively and mitigated through strategic decision-making and accountability.
Effective Risk Management
Reduce the likelihood and impact of security incidents through proactive risk mitigation.
Enhanced Confidence
Demonstrates commitment to risk management, building trust with customers, partners and investors.
Improved Decision Making
Enables informed strategic and operational decisions aligned with business goals and risk profiles.
Organizations often struggle to identify and prioritize evolving risks across systems and business units
Inconsistent, fragmented or ad-hoc risk management approaches across different teams lead to vulnerabilities
Poor risk prioritization can lead to misallocation of efforts and increased likelihood of date breaches
Are your risk management efforts consistent across teams, or do silos create gaps in your security posture?
How confident are you that risks are fully understood and effectively prioritized across your organization?
What processes do you have in place to ensure regulatory compliance and to manage risks of non-compliance?
Privacy Governance
Privacy Operations
Privacy Regulations
Third-Party Risk Management
Risk Based Vulnerability Management
Business Continuity Management
Brand Protection
Incident Management
Merger and Acquisition Due Diligence








Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo






















Benefits of a Change Management





Visit Optiv.com to speak with an advisor that can demonstrate how Optiv Market System can help you optimize your cyber spend.
Schedule a Demo








































































































































Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop

Benchmark your security program across the nine Optiv Market System™ security domains to identify areas that could have the highest impact.
Schedule a Workshop


Related Resource
CISO Periodic Table
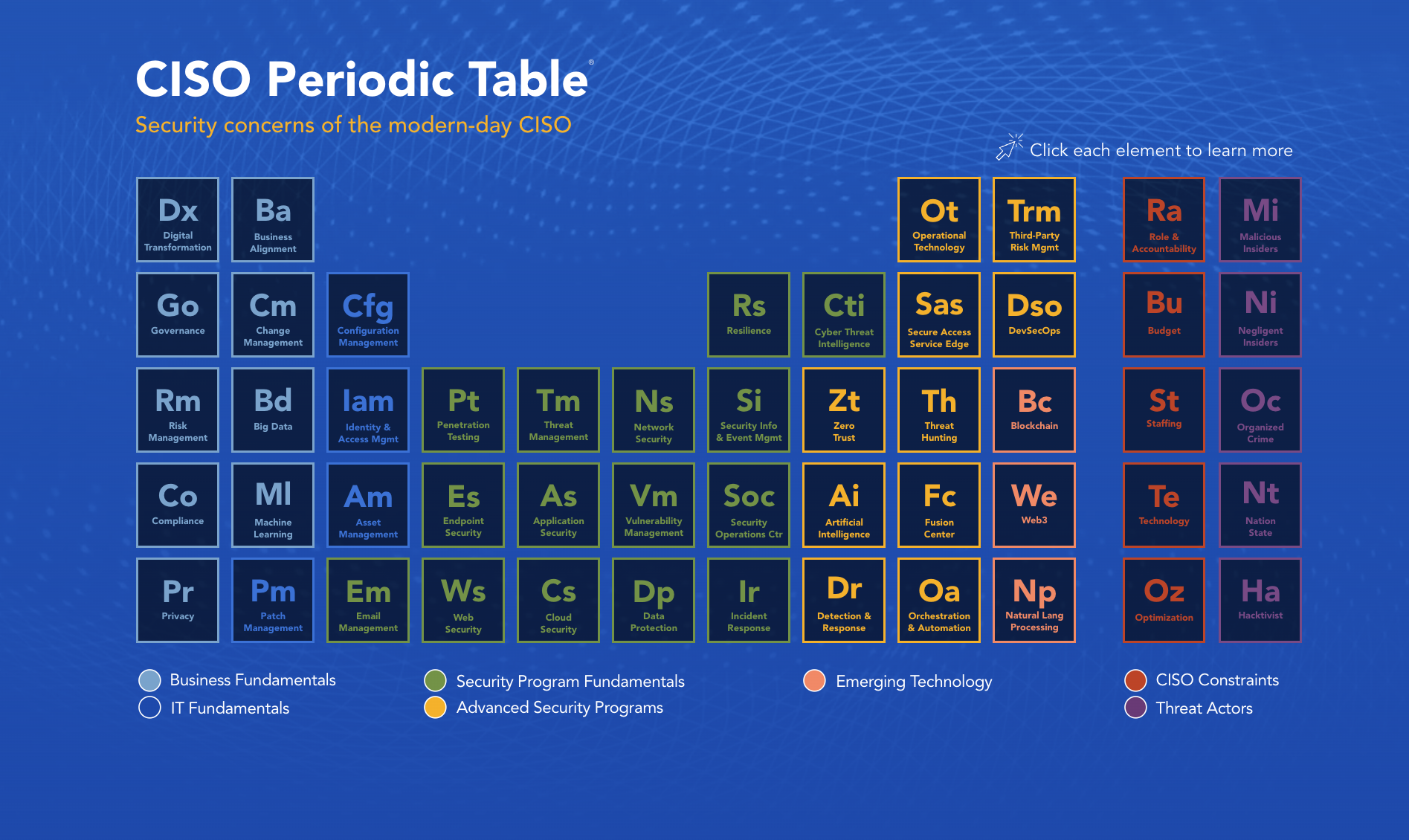
Click on a section to learn more.


Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
Schedule a Workshop
